图书简介
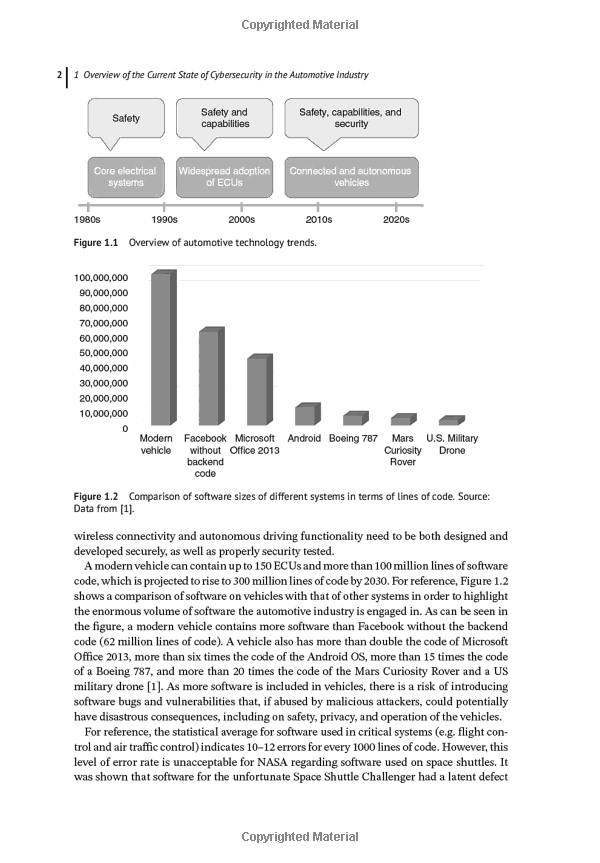
Connectivity and software-based automotive components are now the norm in motor manufacturing, and there can be more than 100 million lines of code in a modern car, making the vehicle highly vulnerable to hacking and other cybersecurity attacks. In response, the automotive industry is investing heavily in security software, effectively creating secure cars. Written by a seasoned automotive expert with international industry expertise, this book introduces readers to the different types of security solutions, with the aim of helping software development and test teams identify vulnerabilities quickly and efficiently. Common problems and pitfalls, based on real-world experiences, are discussed and solutions provided. The aim of the book is to assist auto industry insiders overcome cybersecurity challenges by incorporating security into their software lifecycle to help build more secure and safe cars.
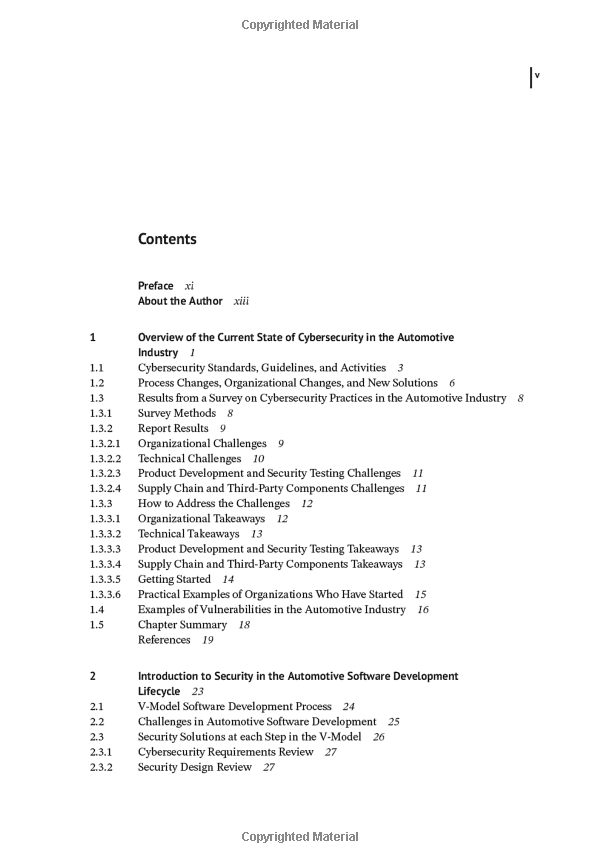
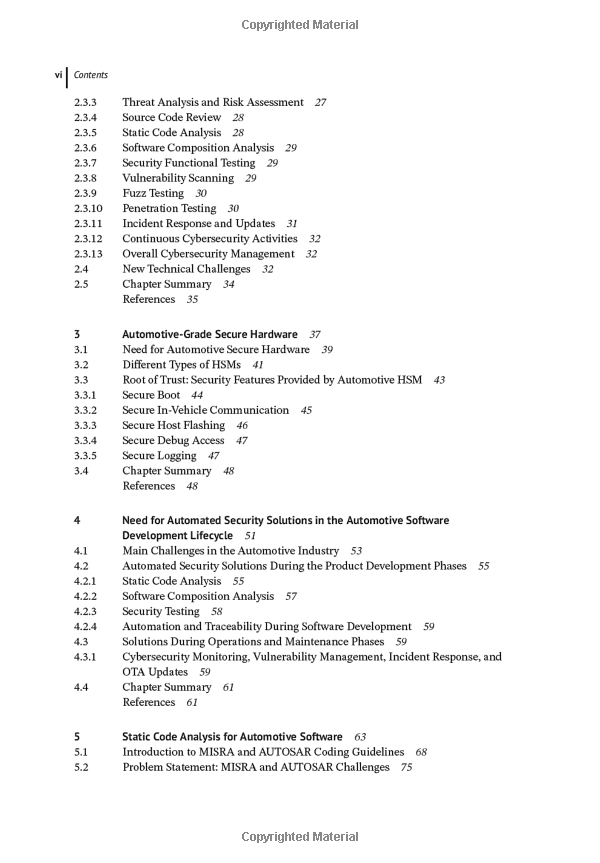
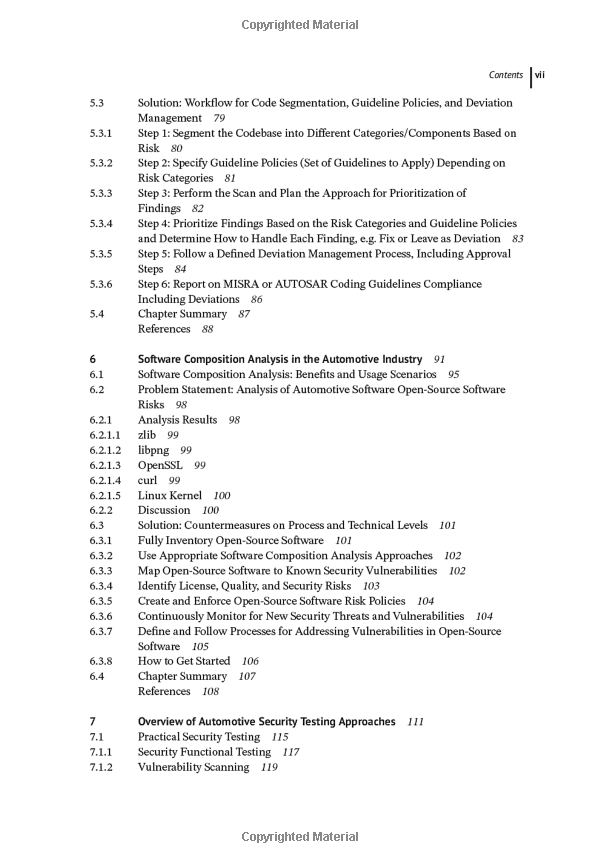
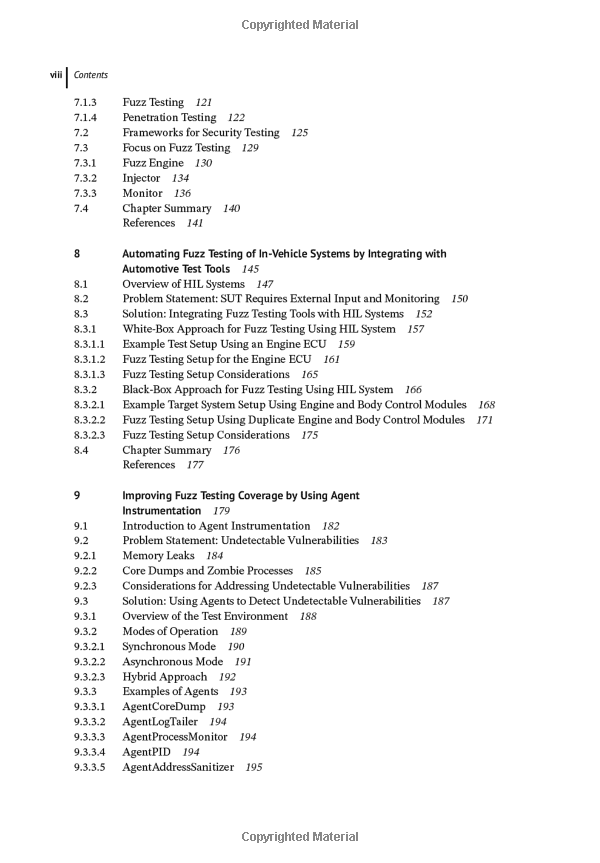
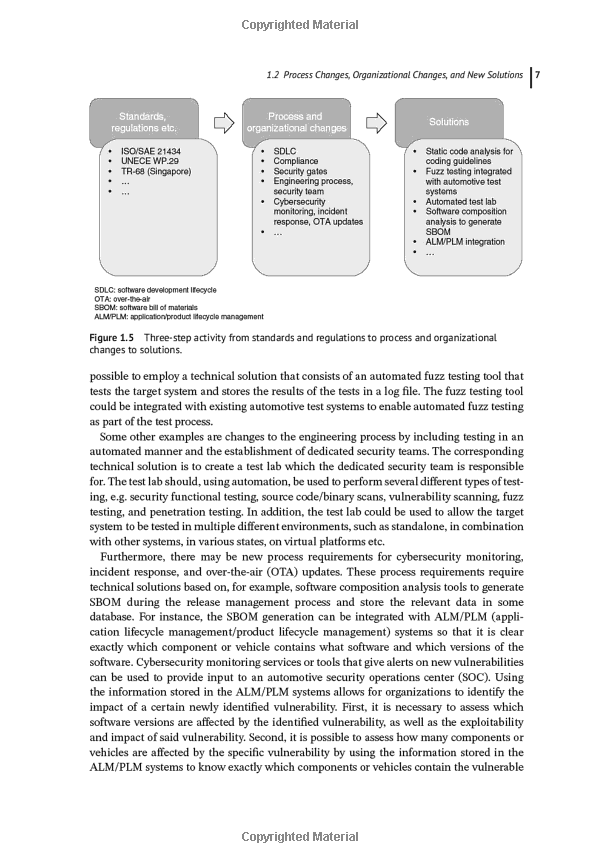
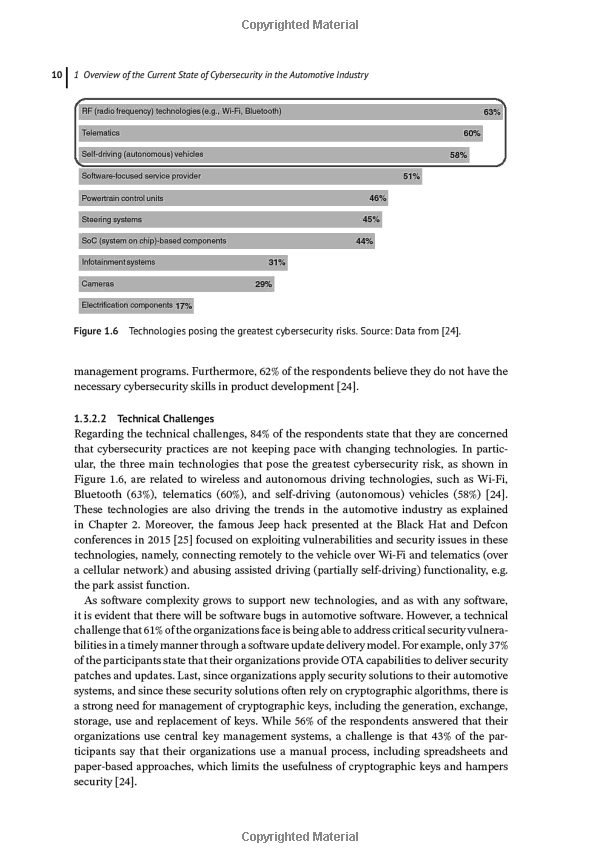
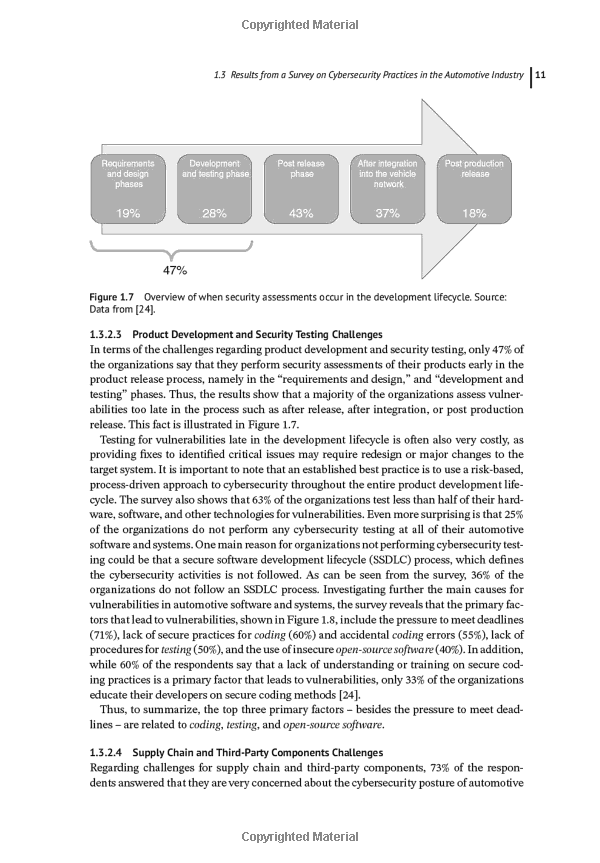
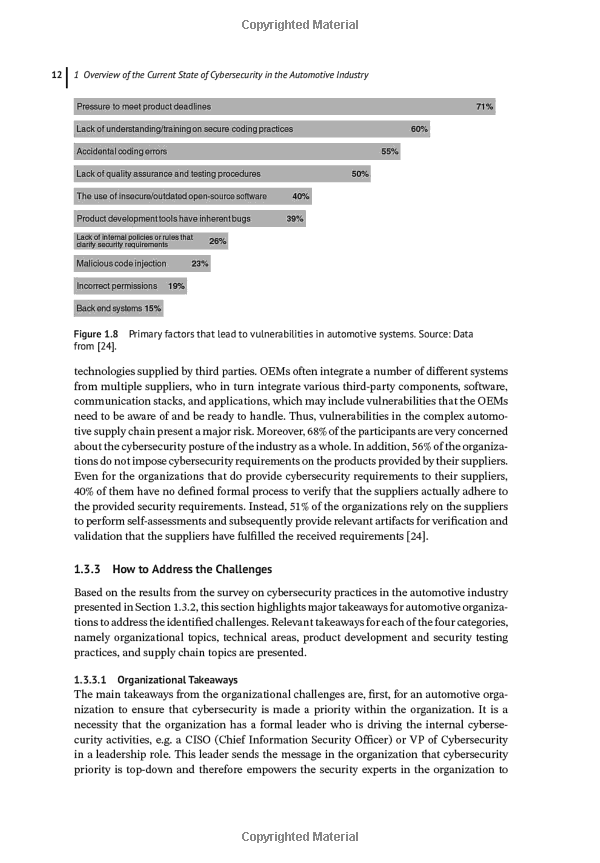
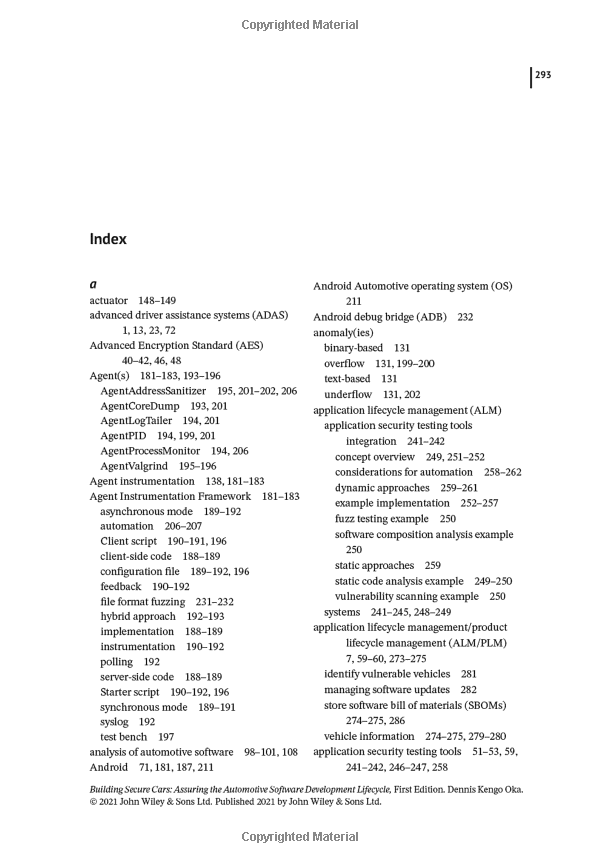
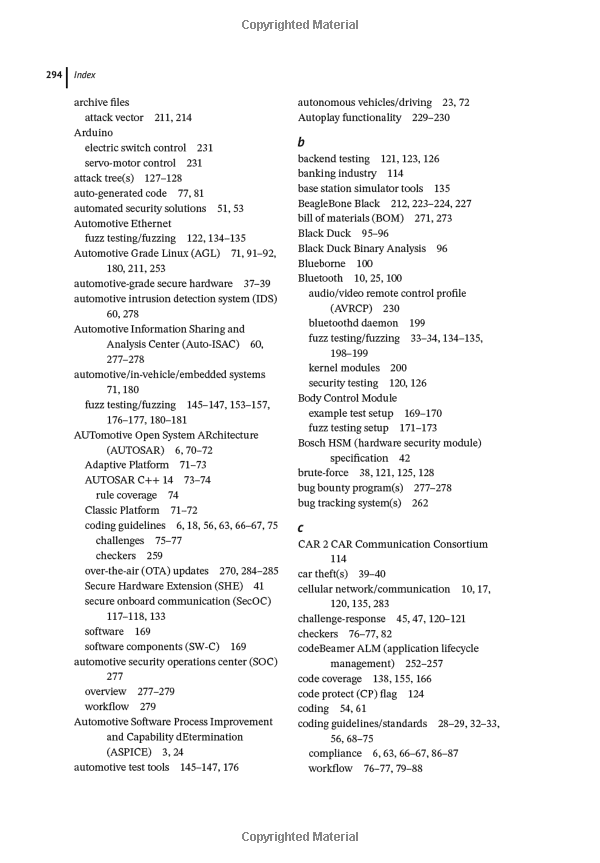
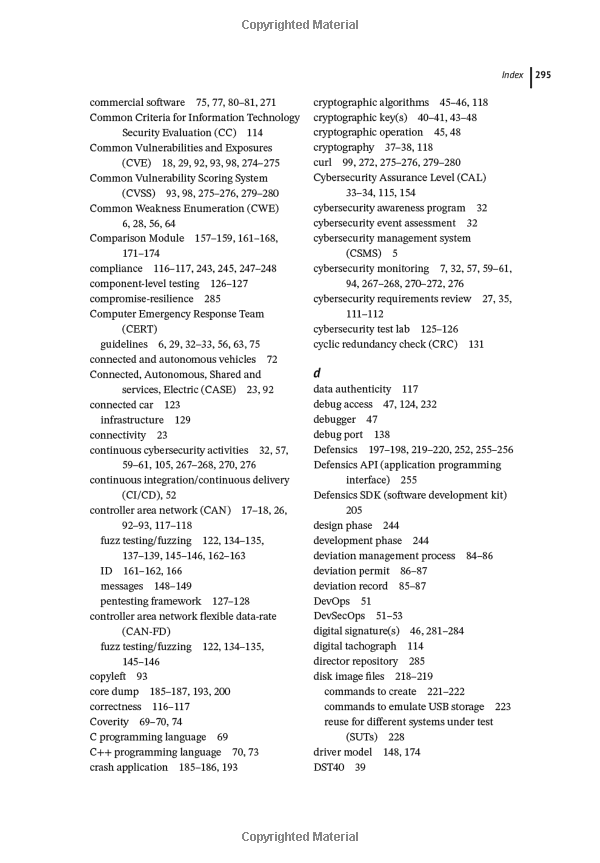
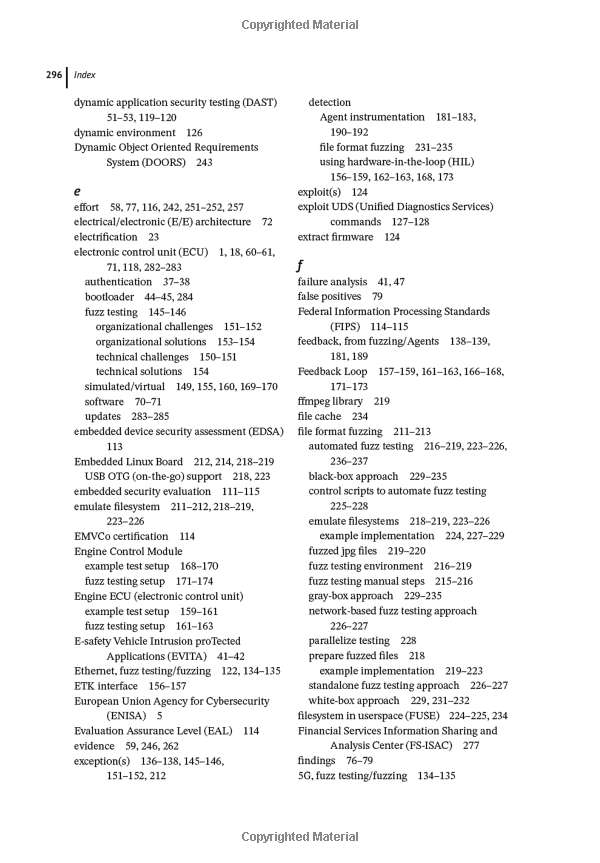
Preface About the Author 1. Overview of the current state of cybersecurity in the automotive industry 1.1. Cybersecurity standards, guidelines, and activities 1.2. Process changes, organizational changes, and new solutions 1.3. Results from a survey on cybersecurity practices in the automotive industry 1.3.1. Survey methods 1.3.2. Report results 1.3.2.1. Organizational challenges 1.3.2.2. Technical challenges 1.3.2.3. Product development and security testing challenges 1.3.2.4. Supply chain and third-party components challenges 1.3.3. How to address the challenges 1.3.3.1. Organizational takeaways 1.3.3.2. Technical takeaways 1.3.3.3. Product development and security testing takeaways 1.3.3.4. Supply chain and third-party components takeaways 1.3.3.5. Getting started 1.3.3.6. Practical examples of organizations who have started 1.3.3.7. 1.4. Examples of vulnerabilities in the automotive industry 1.5. Chapter summary References 2. Introduction to security in the automotive software development lifecycle 2.1. V-model software development process 2.2. Challenges in the automotive software development 2.3. Security solutions at each step in the V-model 2.3.1. Cybersecurity requirements review 2.3.2. Security design review 2.3.3. Threat analysis and risk assessment 2.3.4. Source code review 2.3.5. Static code analysis 2.3.6. Software composition analysis 2.3.7. Functional security testing 2.3.8. Vulnerability scanning 2.3.9. Fuzz testing 2.3.10. Penetration testing 2.3.11. Incident response and updates 2.3.12. Continuous cybersecurity activities 2.3.13. Overall cybersecurity management 2.4. New technical challenges 2.5. Chapter summary References 3. Automotive-grade secure hardware 3.1. Need for automotive secure hardware 3.2. Different types of HSMs 3.3. Root of trust: security features provided by automotive HSM 3.3.1. Secure boot 3.3.2. Secure onboard communication 3.3.3. Secure host flashing 3.3.4. Secure debug access 3.3.5. Secure logging 3.4. Chapter summary References 4. Need for automated security solutions in the automotive software development lifecycle 4.1. Main challenges in the automotive industry 4.2. Automated security solutions during the product development phases 4.2.1. Static code analysis 4.2.2. Software composition analysis 4.2.3. Security testing 4.2.4. Automation and traceability during software development 4.3. Solutions during operations and maintenance phases 4.3.1. Cybersecurity monitoring, vulnerability management, incident response and OTA updates 4.4. Chapter summary References 5. Static code analysis for automotive software 5.1. Introduction to MISRA and AUTOSAR coding guidelines 5.2. Problem statement: MISRA and AUTOSAR challenges 5.3. Solution: Workflow for code segmentation, guideline policies, and deviation management 5.3.1. Step one: Segmenting the codebase 5.3.2. Step two: Specify guideline policies 5.3.3. Step three: Perform the scan and plan the approach for prioritization of findings 5.3.4. Step four: Prioritize findings based on the risk categories and rules and determine how to handle each finding, e.g., fix or leave as deviation 5.3.5. Step five: Follow a defined deviation management process 5.3.6. Step six: Report on MISRA or AUTOSAR including deviations 5.4. Chapter summary References 6. Software composition analysis in the automotive industry 6.1. Software composition analysis, benefits, usage scenarios 6.2. Problem statement: Analysis of automotive software open-source software risks 6.2.1. Analysis results 6.2.1.1. zlib 6.2.1.2. libpng 6.2.1.3. Openssl 6.2.1.4. curl 6.2.1.5. Linux kernel 6.2.2. Discussion 6.3. Solution: Countermeasures on process and technical levels 6.3.1. Fully inventory open-source software 6.3.2. Use appropriate software composition analysis approaches 6.3.3. Map open-source software to known security vulnerabilities 6.3.4. Identify license, quality, and security risks 6.3.5. Create and enforce open-source software risk policies 6.3.6. Continuously monitor for new security threats and vulnerabilities 6.3.7. Define and follow processes for addressing vulnerabilities in open-source software 6.3.8. How to get started 6.4. Chapter summary References 7. Overview of automotive security testing approaches 7.1. Practical security testing 7.1.1. Functional security testing 7.1.2. Vulnerability scanning 7.1.3. Fuzz testing 7.1.4. Penetration testing 7.2. Frameworks for security testing 7.3. Focus on fuzz testing 7.3.1. Fuzz engine 7.3.2. Injector 7.3.3. Monitor 7.4. Chapter summary References 8. Automating fuzz testing of in-vehicle systems by integrating with automotive test tools 8.1. HIL (hardware-in-the-loop) systems 8.2. Problem statement: SUT requires external input and monitoring 8.3. Solution: Integrating fuzz testing tools with HIL systems 8.3.1. White-box approach for fuzz testing using HIL System 8.3.1.1. Example test setup using an Engine ECU 8.3.1.2. Fuzz testing setup for the Engine ECU 8.3.1.3. Fuzz test setup considerations 8.3.2. Black-box approach for fuzz testing using HIL System 8.3.2.1. Example target system setup using engine and body control modules 8.3.2.2. Fuzz testing setup using duplicate engine and body control modules 8.3.2.3. Fuzz test setup considerations 8.4. Chapter Summary References 9. Improving fuzz testing coverage by using Agent instrumentation 9.1. Introduction to Agent instrumentation 9.2. Problem statement: Undetectable vulnerabilities 9.3. Solution: Using agents to detect these vulnerabilities 9.3.1. Overview of test environment 9.3.2. Modes of operation 9.3.2.1. Synchronous mode 9.3.2.2. Asynchronous mode 9.3.3. Examples of agents 9.3.3.1. AgentCoreDump 9.3.3.2. AgentLogTailer 9.3.3.3. AgentProcessMonitor 9.3.3.4. AgentPID 9.3.3.5. AgentAddressSanitizer 9.3.3.6. AgentValgrind 9.3.3.7. An example config.json configuration file 9.3.4. Example results from Agent instrumentation 9.3.4.1. Bluetooth fuzz testing 9.3.4.2. Wi-Fi fuzz testing 9.3.4.3. MQTT fuzzing 9.3.4.4. File format fuzz testing 9.3.5. Applicability and automation 9.4. Chapter summary References 10. Automating file fuzzing over USB for automotive systems 10.1. Need for file format fuzzing 10.2. Problem statement: Manual process for file format fuzzing 10.3. Solution: Emulated filesystems to automate file format fuzzing 10.3.1. System Architecture Overview 10.3.2. Phase one implementation example: Prepare fuzzed files 10.3.3. Phase two implementation example: Automatically emulate filesystems 10.3.4. Automating user input 10.3.5. Monitor for exceptions 10.4. Chapter summary References 11. Automation and traceability by integrating application security testing tools into ALM systems 11.1. Introduction to ALM (application lifecycle management) systems 11.2. Problem statement: Tracing secure software development activities and results to requirements and automating application security testing 11.3. Solution: Integrating application security testing tools with ALM systems 11.3.1. Concept 11.3.1.1. Static code analysis - example 11.3.1.2. Software composition analysis - example 11.3.1.3. Vulnerability scanning - example 11.3.1.4. Fuzz testing - example 11.3.1.5. Concept overview 11.3.2. Example implementation 11.3.3. Considerations 11.4. Chapter summary References 12. Continuous cybersecurity monitoring, vulnerability management, incident response, and secure OTA (over-the-air) updates 12.1. Need for cybersecurity monitoring and secure OTA updates 12.2. Problem statement: Software inventory, monitoring vulnerabilities, and vulnerable vehicles 12.3. Solution: Release management, monitoring and tracking, and secure OTA updates 12.3.1. Release management 12.3.2. Monitoring and tracking 12.3.3. Secure OTA updates 12.4. Chapter summary References 13. Summary and Next Steps Index
Trade Policy 买家须知
- 关于产品:
- ● 正版保障:本网站隶属于中国国际图书贸易集团公司,确保所有图书都是100%正版。
- ● 环保纸张:进口图书大多使用的都是环保轻型张,颜色偏黄,重量比较轻。
- ● 毛边版:即书翻页的地方,故意做成了参差不齐的样子,一般为精装版,更具收藏价值。
关于退换货:- 由于预订产品的特殊性,采购订单正式发订后,买方不得无故取消全部或部分产品的订购。
- 由于进口图书的特殊性,发生以下情况的,请直接拒收货物,由快递返回:
- ● 外包装破损/发错货/少发货/图书外观破损/图书配件不全(例如:光盘等)
并请在工作日通过电话400-008-1110联系我们。
- 签收后,如发生以下情况,请在签收后的5个工作日内联系客服办理退换货:
- ● 缺页/错页/错印/脱线
关于发货时间:- 一般情况下:
- ●【现货】 下单后48小时内由北京(库房)发出快递。
- ●【预订】【预售】下单后国外发货,到货时间预计5-8周左右,店铺默认中通快递,如需顺丰快递邮费到付。
- ● 需要开具发票的客户,发货时间可能在上述基础上再延后1-2个工作日(紧急发票需求,请联系010-68433105/3213);
- ● 如遇其他特殊原因,对发货时间有影响的,我们会第一时间在网站公告,敬请留意。
关于到货时间:- 由于进口图书入境入库后,都是委托第三方快递发货,所以我们只能保证在规定时间内发出,但无法为您保证确切的到货时间。
- ● 主要城市一般2-4天
- ● 偏远地区一般4-7天
关于接听咨询电话的时间:- 010-68433105/3213正常接听咨询电话的时间为:周一至周五上午8:30~下午5:00,周六、日及法定节假日休息,将无法接听来电,敬请谅解。
- 其它时间您也可以通过邮件联系我们:customer@readgo.cn,工作日会优先处理。
关于快递:- ● 已付款订单:主要由中通、宅急送负责派送,订单进度查询请拨打010-68433105/3213。
本书暂无推荐
本书暂无推荐